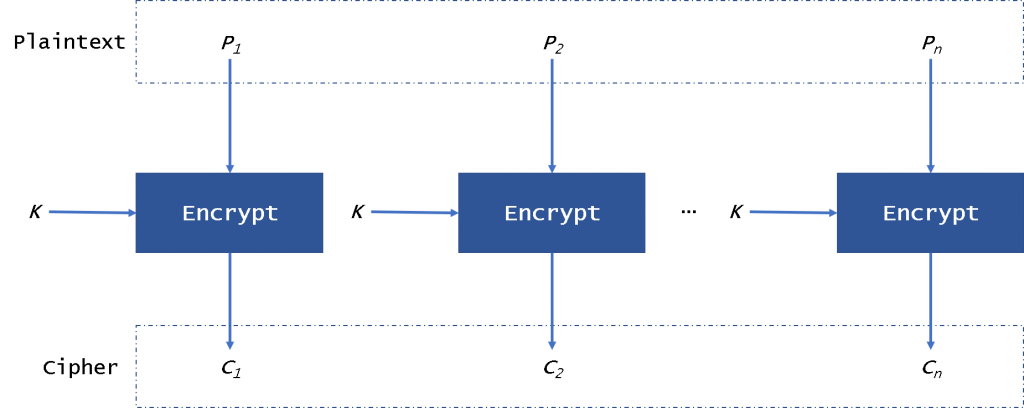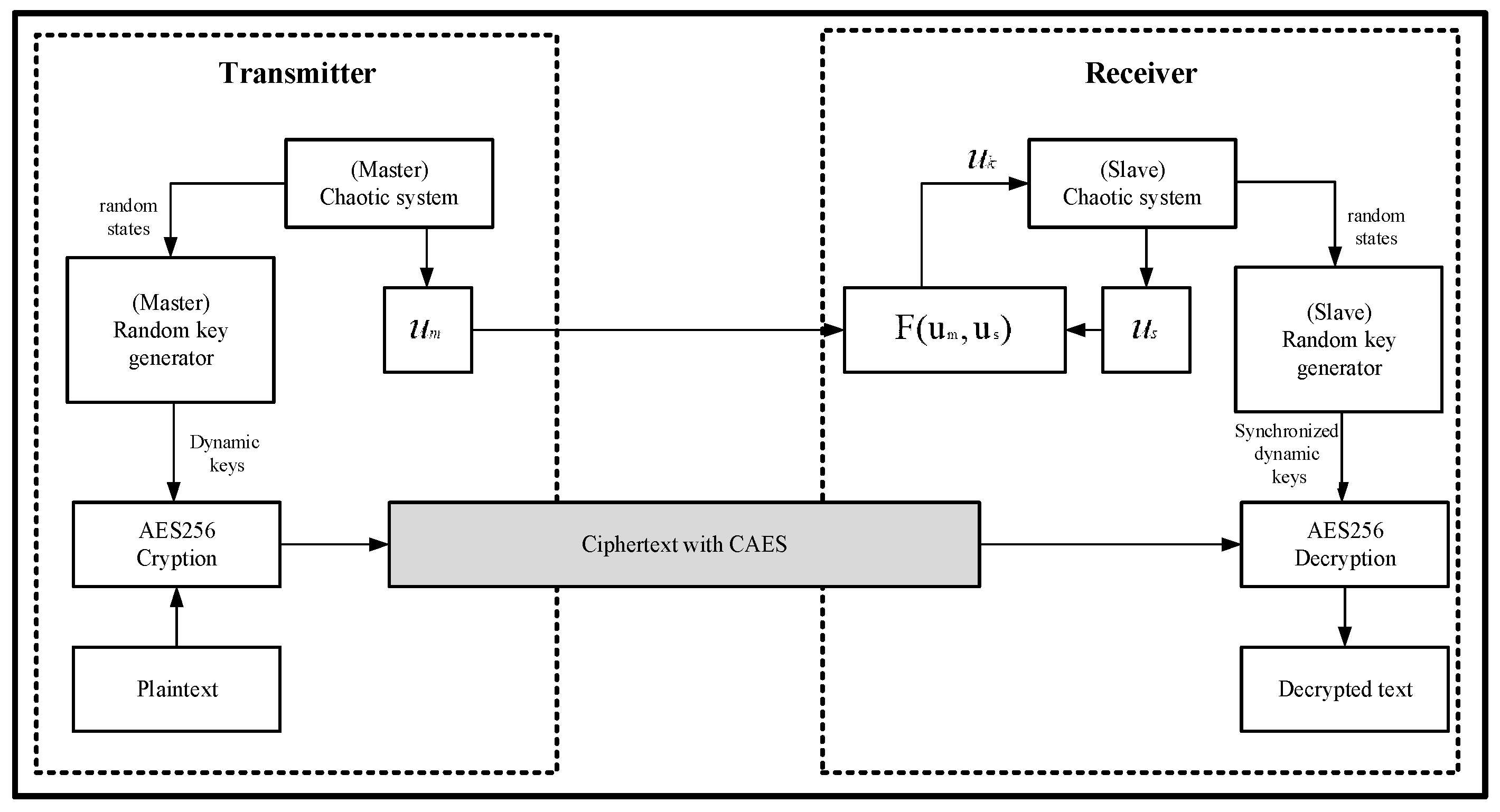
Applied Sciences | Free Full-Text | Chaos-Based Synchronized Dynamic Keys and Their Application to Image Encryption with an Improved AES Algorithm
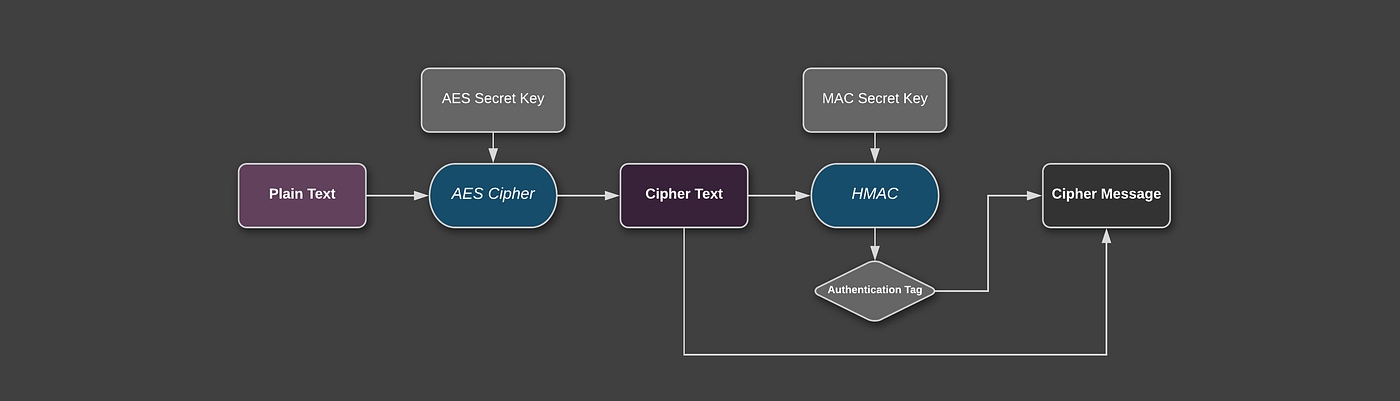
Security Best Practices: Symmetric Encryption with AES in Java and Android: Part 2: AES-CBC + HMAC | by Patrick Favre | ProAndroidDev
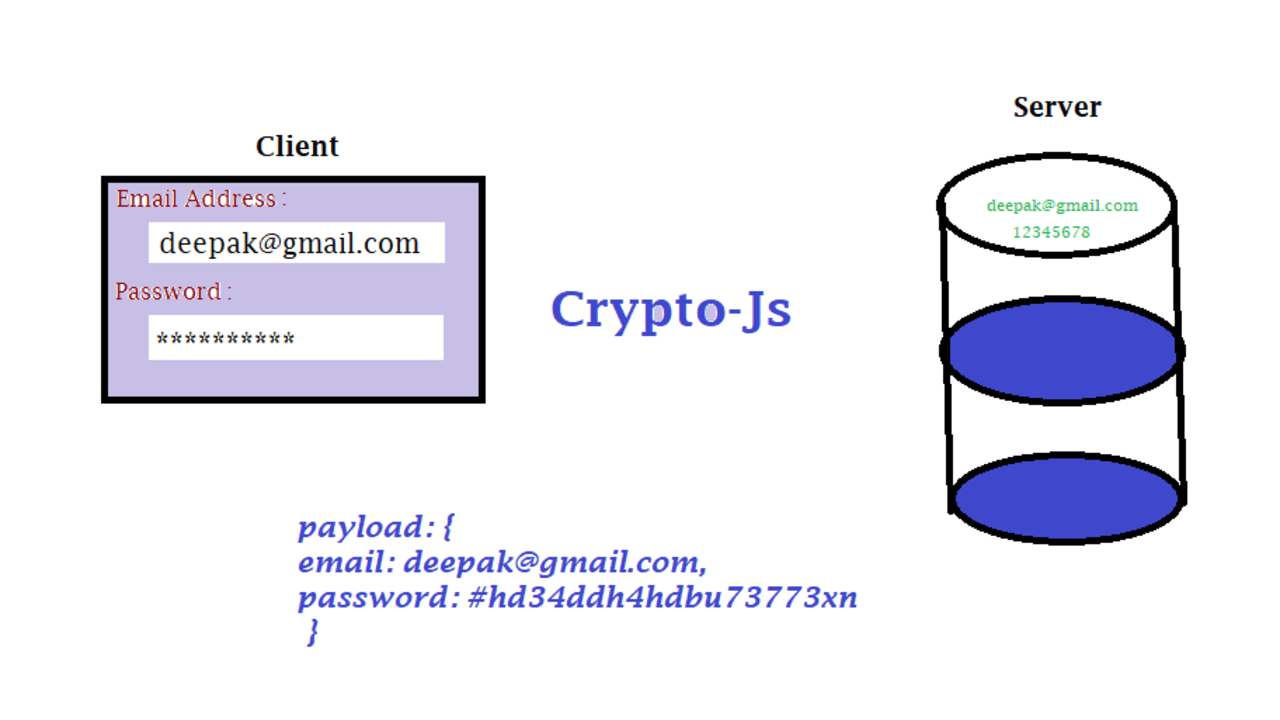
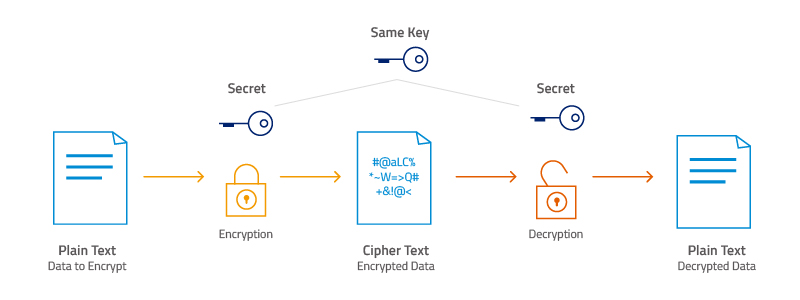
End-to-End Data Security:Shielding API Payloads through CryptoJS and Java AES-256 Encryption” | by Shivam Jaswal | Medium

Electronics | Free Full-Text | Magniber v2 Ransomware Decryption: Exploiting the Vulnerability of a Self-Developed Pseudo Random Number Generator
Crypto.createDecipheriv() using aes-256-cbc on an encrypted XML document · Issue #2896 · nodejs/help · GitHub
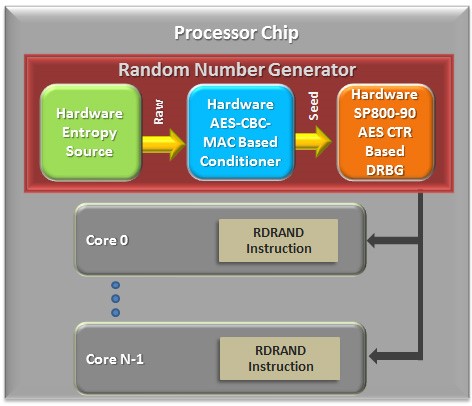
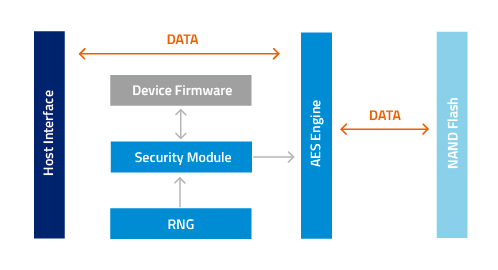
Intel® Hardware-based Security Technologies Bring Differentiation to Biometrics Recognition Applications Part 2 - CodeProject
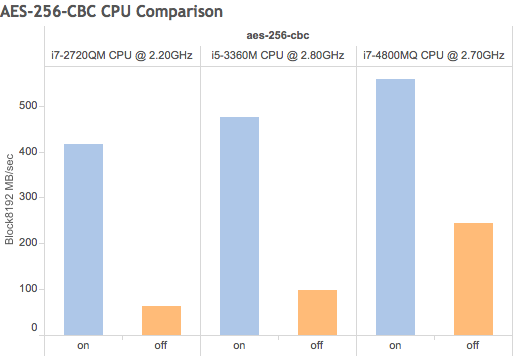
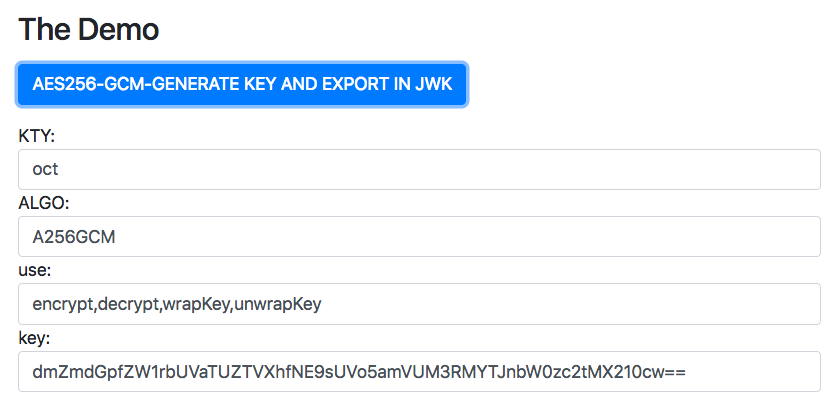
Using your existing hardware, Forward Secrecy and AES-NI to enhance system speed and security for free